Lock In Proof, Unlock Trust: Securing All Critical Commerce With Proof
4.7
(392)
Write Review
More
$ 8.99
In stock
Description

IBM Cloud Hyper Protect Virtual Servers

Capabilities - Identity Verification

Ethical Lock-Pickers Team Up With Manufacturers to Solve Major Security Flaws - Bloomberg
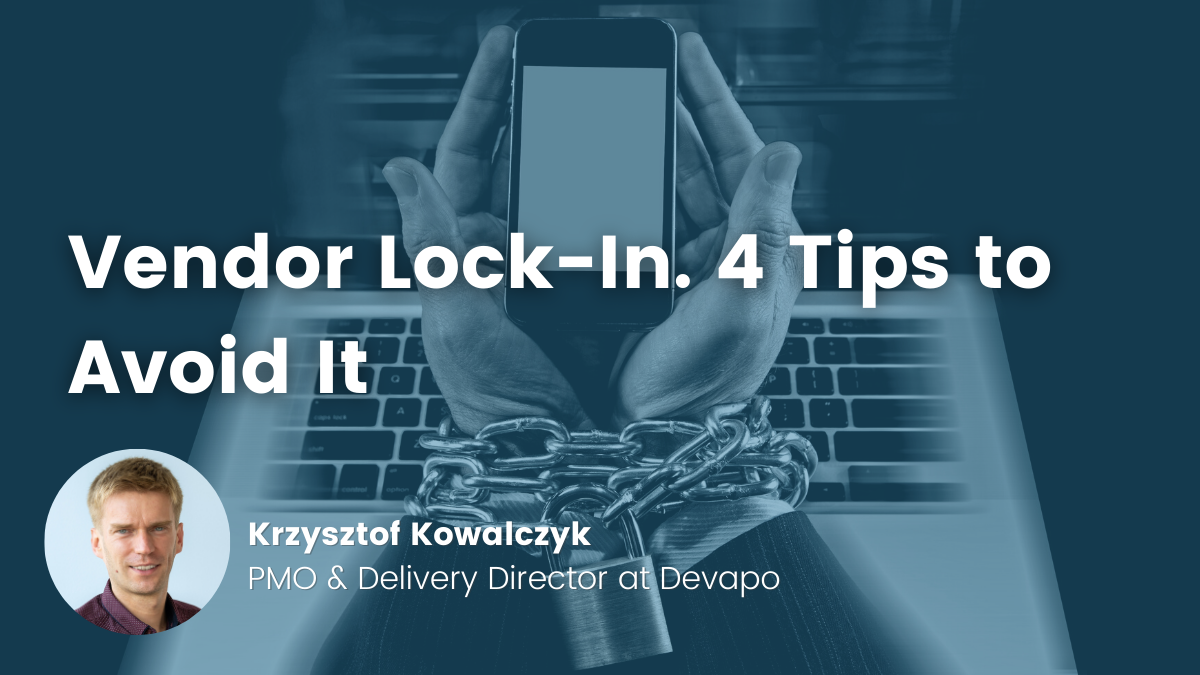
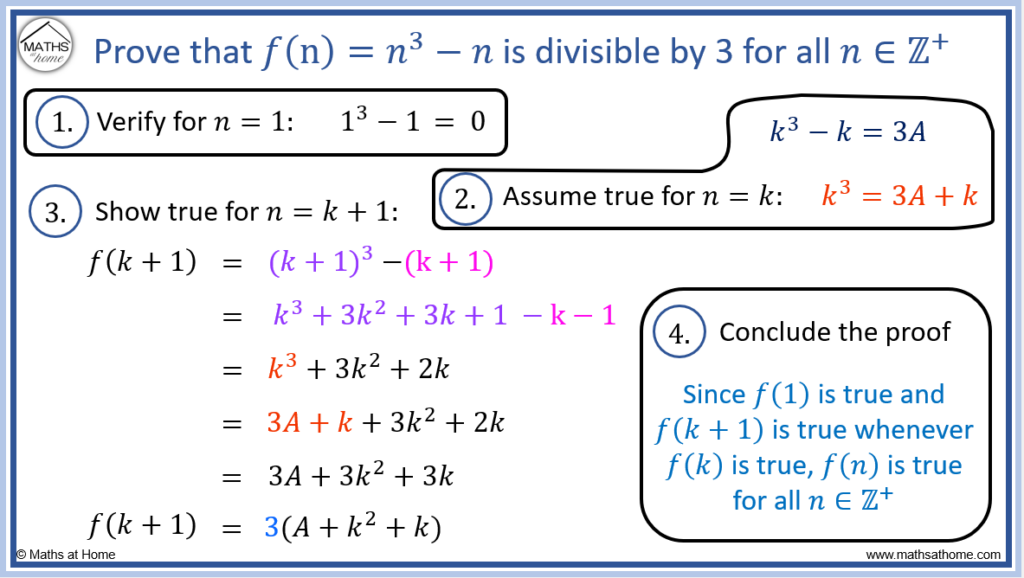
Tips to Avoid Vendor Lock-In and Achieve Long-Term Success

8 cloud computing trends reshaping the industry in 2024 - N-iX

Blog Notarize

Application Security Standards

What Are Verifiable Credentials? How They Build Digital Trust

Blog Notarize

This Week at Notarize: #DIW2021 edition 🎥 Nicole Booth joins
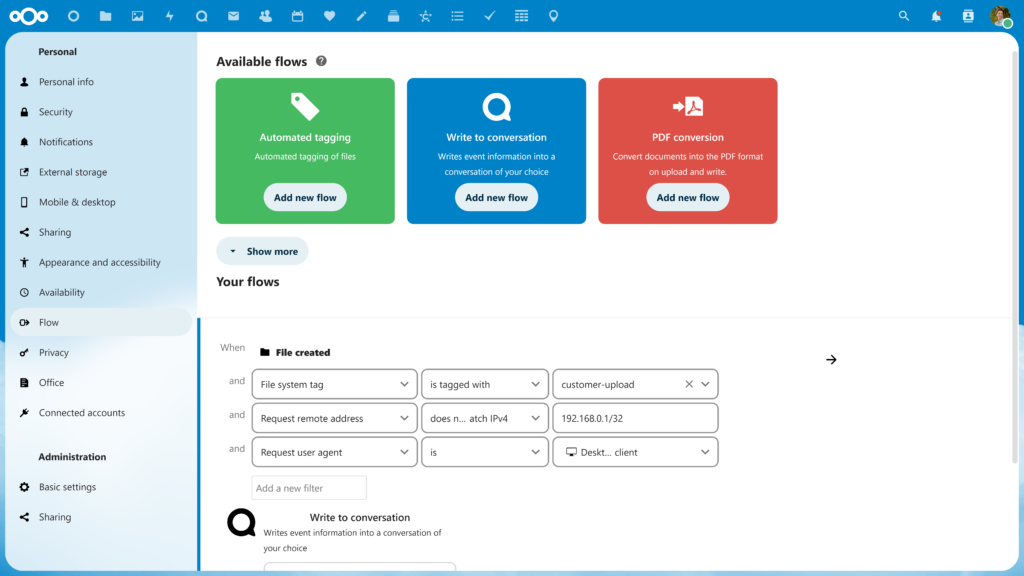
Nextcloud features that put you in control

How to Develop Internal Controls to Mitigate IT Security Risks - Hyperproof

How to theft-proof your smartphone and the data on it

Top 10 Continuous Security Monitoring (CSM) Tools for 2024
Related products
You may also like